Install Maldetect Cpanel
Instalação e Configuração do Linux Malware Detect (Maldet) no cPanel

Instalação
Para instalar o Maldet no servidor cPanel, siga os seguintes passos:
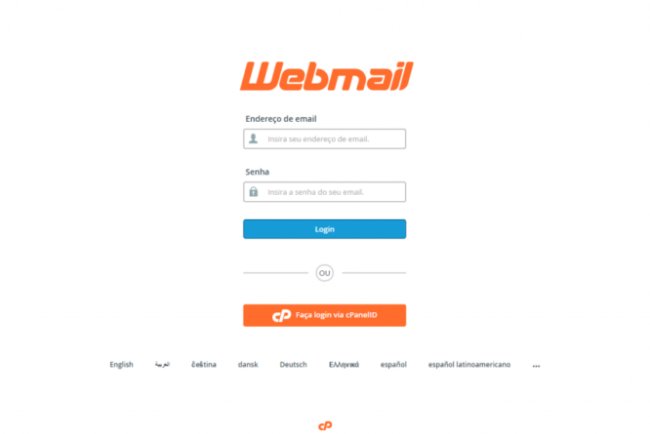
- Faça login no servidor cPanel via SSH como usuário root.
- Execute os comandos abaixo:
cd /usr/local/src/
wget http://www.webchamp.com.br/downloads/maldetect-current.tar.gz
tar -xzf maldetect-current.tar.gz
cd maldetect-*
sh ./install.sh
Atualizando a Aplicação
Para atualizar manualmente o Maldet, execute:
maldet -d
maldet -u
Configurando o Linux Malware Detect (Maldet)
Por padrão, todas as opções estão comentadas no arquivo de configuração. Configure-o conforme suas necessidades. Antes de fazer alterações, vamos revisar cada opção em detalhes.
- Abra o arquivo
/usr/local/maldetect/conf.maldete faça as alterações necessárias:
nano /usr/local/maldetect/conf.maldet- email_alert: Se deseja receber alertas por e-mail, defina como 1.
- email_addr: Adicione seu endereço de e-mail para receber alertas de malware.
- quarantine_hits: Ação padrão de quarentena para detecções de malware, deve ser definido como 1.
- quarantine_clean: Limpeza de injeções de malware detectadas, deve ser definido como 1.
- quarantine_suspend_user: Ação padrão de suspensão para usuários com detecções, defina conforme suas necessidades.
- quarantine_suspend_user_minuid: ID mínimo de usuário que pode ser suspenso.
- Altere o tamanho máximo do arquivo para ser incluído na varredura:
# O tamanho máximo de arquivo para ser incluído na varredura
# use man find para valores aceitos
# [ alterá-lo pode impactar na performance da varredura ]
maxfilesize="768k"
Altere 768k para 1024k.
Executando a Varredura Completa em Diretórios Home dos Usuários
Primeiramente, sugiro uma varredura completa nos diretórios home dos usuários para detectar e limpar malware:
maldet -a /home/?
Depois, você pode optar por escanear apenas arquivos .php, por exemplo:
maldet --include-regex ".*\.php$" -a /home/?/public_html
Acionando a Varredura
Para monitorar todos os usuários, use o comando abaixo:
# maldet -m usersResolvendo Erros
Se encontrar algum erro, instale o pacote abaixo com o comando:
yum install inotify-tools -yQual é a sua reação?